The Artificial Intelligence and Data Act… coming soon to AI near you
In June, 2022, the Government introduced Bill C-27, an Act to enact the Consumer Privacy Protection Act, the Personal Information and Data Protection Tribunal Act, and the Artificial Intelligence and Data Act. A major component of this proposed legislation is a brand new law on artificial intelligence. This will be, if passed, the first Canadian law to regulate AI systems.
The stated aim of the Artificial Intelligence and Data Act (AIDA) is to regulate international and interprovincial trade and commerce in artificial intelligence systems. The Act requires the adoption of measures to mitigate “risks of harm” and “biased output” related to something called “high-impact systems“.
Ok, so how will this work? First, the Act (since it’s federal legislation) applies to “regulated activity” which refers to specific activities carried out in the course of international or interprovincial trade and commerce. That makes sense since that’s what falls into the federal jurisdiction. Think banks and airlines, for sure, but the scope will be wider than that since any use of a system by private sector organizations to gather and process data across provincial boundaries will be caught. The regulated activities are defined as:
- (a) processing or making available for use any data relating to human activities for the purpose of designing, developing or using an artificial intelligence system;
- (b) designing, developing or making available for use an artificial intelligence system or managing its operations.
That is a purposely broad definition which is designed to catch both the companies that use these systems, and providers of such systems, as well as data processors who deploy AI systems in the course of data processing, where such systems are used in the course of international or interprovincial trade and commerce.
The term “artificial intelligence system” is also broadly defined and captures any “technological system that, autonomously or partly autonomously, processes data related to human activities through the use of a genetic algorithm, a neural network, machine learning or another technique in order to generate content or make decisions, recommendations or predictions.”
For anyone carrying out a “regulated activity” in general, there are record keeping obligations, and regulations regarding the handling of anonymized data that is used in the course of such activities.
For those who are responsible for so-called “high-impact systems“, there are special requirements. First, a provider or user of such a system is responsible to determine if their system qualifies as a “high-impact system” under AIDA (something to be defined in the regulations).
Those responsible for such “high-impact systems” must, in accordance with the regulations, establish measures to identify, assess and mitigate the risks of harm or biased output that could result from the use of the system, and they must also monitor compliance with these mitigation measures.
There’s more: anyone who makes a “high-impact system” available, or who manages the operation of such a system, must also publish a plain-language description of the system that includes an explanation of:
- (a) how the system is intended to be used;
- (b) the types of content that it is intended to generate and the decisions, recommendations or predictions that it is intended to make; and
- (c) the mitigation measures.
- (d) Oh, and any other information that may be prescribed by regulation in the future.
The AIDA sets up an analysis of “harm” which is defined as:
- physical or psychological harm to an individual;
- damage to an individual’s property; or
- economic loss to an individual.
If there is a risk of material harm, then those using these “high-impact systems” must notify the Minister. From here, the Minister has order-making powers to:
- Order the production of records
- Conduct audits
- Compel any organization responsible for a high-impact system to cease using it, if there are reasonable grounds to believe the use of the system gives rise to a “serious risk of imminent harm”.
The Act has other enforcement tools available, including penalties of up to 3% of global revenue for the offender, or $10 million, and higher penalties for more serious offences, up to $25 million.
If you’re keeping track, the Act requires an assessment of:
- plain old “harm” (Section 5),
- “serious harm to individuals or harm to their interests” (Section 4),
- “material harm” (Section 12),
- “risks of harm” (Section 8),
- “serious risk of imminent harm” (Sections 17 and 28), and
- “serious physical or psychological harm” (Section 39).
All of which is to be contrasted with the well-trodden legal analysis around the term “real risk of significant harm” which comes from privacy law.
I can assure you that lawyers will be arguing for years over the nuances of these various terms: what is the difference between “harm” and “material harm”, “risk” versus “serious risk”? and what is “serious harm” versus “material harm” versus “imminent harm”? …and what if one of these species of “harm” overlaps with a privacy issue which also triggers a “real risk of significant harm” under federal privacy laws? All of this could be clarified in future drafts of Bill C-27, which would make it easier for lawyers to advise their clients when navigating the complex legal obligations in AIDA
Stay tuned. This law has some maturing to do, and much detail is left to the regulations (which are not yet drafted).
Calgary – 16:30 MT
No commentsBeer Brand Battle at the 100th Meridian
By Richard Stobbe
A Canadian band, The Tragically Hip, has sued a brewer for the use of a beer name that mimics the title of one of the band’s popular songs.
Mill Street Brewery, a brand owned by Anheuser-Busch InBev (the world’s largest brewer), has a beer branded as “100th Meridian Organic Amber Lager” .
This sounds familiar to fans of the The Hip, who will recall rockin’ out to the opening power chords of the 1992 hit entitled “At The Hundredth Meridian” from the Fully Completely album.
Does the name of a song from the 1990s take on the attributes of a trademark? Does the use of song title create a false association with the band, such that the band’s trademark rights are infringed? What if the name of the song ( “At The Hundredth Meridian” ) is not identical to the beer name (“100th Meridian”)? Does it make a difference if other brewers have given a nod to The Hip (Fully Completely IPA from Phillips Brewing, Ahead by a Century IPA, Tragically Hopped Double IPA, what’s with all the IPAs? heck there’s even a 50 Mission Cap Brewing Co.!).
This week, The Hip sued Trillium Beverage the brewer of the Mill Street product (Trillium is owned by Labatt Brewing Company, which in turn is owned by the conglomerate AB InBev), claiming trademark infringement. This is a tricky one for a couple of reasons, particularly since the brewer owns a registered trademark for “100th MERIDIAN” for beer. The Hip will face an uphill battle there. However, Mill Street didn’t do itself any favours by posting pictures on social media of the beer next to Tragically Hip albums, clearly suggesting some kind of association.
Related Reading: The Tragically Hip sue Mill Street Brewery over 100th Meridian beer
The lawsuit will likely settle, but if it does go through to a judgement on its merits, it will be an interesting one to watch.
Calgary – February 10, 2021
No commentsClick-Through Agreements
.
By Richard Stobbe
Sierra Trading Post is an Internet retailer of brand-name outdoor gear, family apparel, footwear, sporting goods. Sierra lists comparison prices on its site to show consumers that its goods are competitively priced.
Chen, the plaintiff, sued Sierra, claiming the website’s comparison prices were false, deceptive, or misleading. The internet retailer defended by asserting that the lawsuit should be dismissed: Sierra pointed out that users of its site agreed to binding arbitration in the Terms of Use. Chen countered, arguing that he had never seen the Terms of Use and so they were not binding.
In Chen v. Sierra Trading Post, Inc., 2019 WL 3564659 (W.D. Wash. Aug. 6, 2019), a US court decision, the court reviewed the issues. There was no disagreement that the choice-of-law and arbitration clauses appeared in the Terms of Use. The question, as with so many of these cases, is around the set-up of Sierra’s check-out screen. Were the Terms of Use brought to the attention of the user, so that the user consented to those terms at the point of purchase, thus evidencing a mutual agreement between the parties to be bound by those terms?
Both Canadian and US cases have been tolerant of a range of possibilities for a check-out procedure, and the placement of “click-through” terms. This applies equally to e-commerce sites, software licensing, subscription services, or online waivers. Ideally, the terms are made available for the user to read at the point of checkout, and the user or consumer has a clear opportunity to indicate assent to those terms. In some cases, the courts have accepted terms that are linked, where assent is indicated by a check-box.
While there is no specific bright-line test, the idea is to make it as easy as possible for a consumer to know (1) that there are terms and (2) that they are taking a positive step to agree to those terms.
In this case, STP claimed that Chen would have had notice of the Terms of Use via the website’s “Checkout†page where, a few lines below the “Place my order†button, a line says “By placing your order you agree to our Terms & Privacy Policyâ€. The court noted that “The Consent line contains hyperlinks to STP’s TOU and Privacy Policy.”
On balance, the court agreed to uphold the Terms of Use and compel arbitration. While this was a win for Sierra, the click-through process could easily have been much more robust. For example, rather than “Place my order”, the checkout button could have said said “By Placing my order I agree to the Terms of Use” or a separate radio button could have been placed beside the Terms of Use and Privacy Policy to indicate assent.
Internet retailers, online service providers, software vendors and anyone imposing terms through click-through contracts should ensure that their check-out process is reviewed: make it as easy as possible for a court to agree that those terms are binding.
Calgary – 07:00 MST
No commentsCanadian Site-Blocking Decision
By Richard Stobbe
A streaming service known as “GoldTV” was in the business of rebroadcasting television programing through online broadcasting or streaming services to Canadian consumers. This had the effect of eating into the core business model of traditional Canadian broadcasters such as Bell Media and Rogers. Can a broadcast company fight back against this type of streaming service by seeking a site-blocking order?
Based on copyright infringement allegations, the broadcasters took GoldTV to court and obtained interim court orders. Despite the issuance of the interim and interlocutory injunctions directly against GoldTV, some of the offending services remained accessible, and the alleged infringement continued. Basically, GoldTV remained anonymous and (practically speaking) beyond the reach of the Canadian courts. Bell Media and Rogers then sought an order to compel Canadian ISPs to block access to GoldTV’s sites.
We know that, under Canadian law, non-party actors can be ordered by a Canadian court to take certain steps. In Google Inc. v. Equustek Solutions Inc., 2017 SCC 34 (CanLII), the Supreme Court of Canada approved a court order that required Google to globally de-index the websites of a company in breach of several court orders. The Court affirmed that injunctions can be issued against someone who is not a party to the underlying litigation.
In this recent decision, Bell Media Inc. v. GoldTV.Biz, 2019 FC 1432 (CanLII),  the court confirmed that it can order ISPs, such as Bell Canada, Fido, Telus and Shaw, to block the offending GoldTV sites. Although there are obvious analogies to the Equustek case, the court in GoldTV indicated an order of this nature has not previously issued in Canada but has in other jurisdictions, including the United Kingdom. Equustek involved de-indexing from a search engine, whereas the GoldTV case involves site-blocking. The court issued the site-blocking order, with a 2-year sunset clause.
Teksavvy Solutions (one of the ISPs bound by the order) has appealed this decision to the Federal Court of Appeal (PDF).
Stay tuned.
Calgary – 07:00 MST
No commentsCopyright Fight: Hollywood versus a Film School Project
By Richard Stobbe
In 2015 Pixar, Disney’s animation company, released INSIDE OUT, a feature-length animated film featuring a character whose emotions of Joy, Sadness, Anger, Fear and Disgust take the form of personified characters.  Did Pixar’s 2015 production infringe the copyright in the film school project from fifteen years earlier? That’s what Mr. Pourshian alleges, claiming that he is the owner of copyright in his original screenplay, live theatrical production, and short film, each of which are titled “Inside Out“, and that Pixar infringed those copyrights “by production, reproduction, distribution and communication to the public by telecommunication of the film INSIDE OUTâ€.
This case is more akin to Cinar Corporation v. Robinson, 2013 SCC 73 (CanLII), where the infringement claim did not involve direct cut-and-paste copying, but rather was based on an assessment of the cumulative effect of the features copied from the original work, to determine whether those features amount to a substantial part of the skill and judgment of the original author, expressed in the original work as a whole. This involves a review of whether there is substantial copying of elements like particular visual elements of setting and character, content, theme and pace. Compare this one with Sullivan v. Northwood Media Inc. (Anne with a © : Copyright infringement and the setting of a Netflix series).
The Pourshian case was a preliminary motion about whether the claim can proceed in Canada, or whether it should be heard in the US. The Court found that there was a real and substantial connection in relation to the claims and Ontario, and the case will be permitted to continue against Pixar Animation Studios, Walt Disney Pictures Inc. and Disney Shopping Inc.
If this case proceeds to trial, it will be fascinating to watch.
Mr. Pourshian did pursue a separate claim in California (Pourshian v. Disney, Case No. 5:18-cv-3624), which was voluntarily withdrawn in 2018.
Calgary – 07:00 MST
No commentsPrivacy Update: Transborder Data Flow
By Richard Stobbe
In our post earlier this year (Privacy Update: Will Consent be Required for Outsourcing Canadian Data?) we reviewed the changes proposed by the Office of the Privacy Commissioner of Canada. These changes would have changed the way the Commissioner viewed transborder flows of personal information. Transfer across a border would have been considered a “disclosureâ€, mandating a new consent, as opposed to a “use†which could be covered by the initial consent at the time of collection.Â
In September, after the consultation period ended, the OPC confirmed it will hold to its 2009 Guidelines for Processing Personal Data Across Borders.
This is good news for any Canadian business who uses a service provider outside of the country to process data – such as the use of Gmail for corporate email, or Amazon Web Services (AWS) for data hosting, or the use of a UK company for CRM data processing services. If your company is compliant with the 2009 guidelines, then no change is required.
For advice on cross-border transfers of personal data, please contact us.
Related Reading: OPC Reaffirms 2009 Consent Standard for Cross-Border Data Processing
Calgary – 07:00 MST
No commentsInfringing Trademarks Cannot Remain on the Register
By Richard Stobbe
In a battle between the suitcase makers, the Federal Court of Appeal found that Travelway Group International Ltd. (Travelway), had infringed the trademarks owned by Wenger, and had passed off its own goods as Wenger’s. The Court granted Wenger a declaration of trademark infringement, ordered a permanent injunction prohibiting Travelway from using its infringing marks, and ordered Travelway to destroy or deliver up all wares, packages, labels and advertising material.
Basically, this was a complete victory for the well-known Swiss-cross style Wenger brand, depicted below.
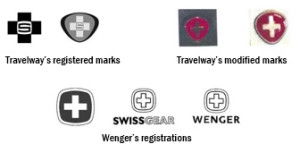
However, the Federal Court of Appeal decision resulted in an anomaly: at the time of the trademark infringement lawsuit in 2013, the trademarks of both Wenger and Travelway were registered in Canada. In the appeal decision, the Court concluded, ultimately, that “each of the Travelway marks is confusing with each of the Wenger marks”, but the Court left the registrations in place, with the result that infringing, invalid trademarks were nevertheless maintained on the register in Canada.
The court in Wenger SA v. Travelway Group International Inc., 2019 FC 1104 (CanLII), corrected this, expunging the Travelway marks.
It’s also worth noting that the Travelway registrations were not found to be void ab initio, and thus benefited from the protection granted by section 19 of the Trademarks Act, which indicates that a registration is a defence to infringement. The court appears to have accepted Travelway’s argument that the protection of section 19 should extend to the variants of the Travelway marks, given that the Federal Court of Appeal found them to be permissible variants.
Related Reading: CANADA: Infringing Trademark Registrations Must Be Expunged, Court Finds
Calgary – 07:00 MST
No commentsCopyright and Code: Can a Software Developer Take a Shortcut?
By Richard Stobbe
Let’s say an employee is hired as a software engineer to develop an application for the employer.  The employee completes the project, and the software program is launched as a commercial product. Copyright is registered in the software, showing the employee as author, and the employer as owner. So far so good.
The employee leaves, and her company launches its own software product, which seems to compete directly with the software that was created for her former employer. Ok, now we have a problem.
Or do we? These are the basic facts in the interesting case of Knowmadics v. Cinnamon and LDX Inc., 2019 ONSC 6549 (CanLII), where an ex-employee left her employment in 2017, and within two months of signing a Non-Disclosure Agreement, her company LDX was offering software products that seemed to contain similar features and competed directly with Knowmadics, the former employer.
Knowmadics sued its former employee, claiming that the LDX software infringed the copyright of Knowmadics. The claim also alleged breach of the Employment Agreement, a Subcontractor Agreement, and a Non-Disclosure Agreement.
An analysis of the code showed that there were similarities and overlap between the software written for Knowmadics, the former employer, and the software sold by Ms. Cinnamon, the former employee through her company LDX.  However, Ms. Cinnamon raised a defence that makes perfect sense in light of the way that many software projects evolve: any similarities, the employee argued, were due to the simple fact that she used her own prior code in developing the program for Knowmadics, during her employment, and that same code was incorporated into a database that she wrote for an earlier client, and the same code was subsequently incorporated into the software she wrote for her own company, LDX. So of course it has similar features, it’s all from the code originally authored by the same developer.
To borrow from the court’s analysis: “The relevant issue as far as the database goes is a legal one for the Court to determine at trial: once Ms. Cinnamon delivered SilverEye to Knowmadics incorporating that prior database without identifying that she was doing so, and Knowmadics copyrighted SilverEye with that database code and schema, was Ms. Cinnamon then permitted under copyright law or her agreements with Knowmadics to take a shortcut and use the same code and schema to create a competing software with the same functionalities? This is a serious issue to be determined at trial…”
The reported decision dealt with a pre-trial injunction application. The order granted by the court simply maintained the status quo pending trial, so the merits of this case are still to be decided. If it does proceed to trial, this case will engage some very interesting issues around copyright, software, originality and licensing of code.
Stay tuned.
Calgary – 07:00 MT
No commentsBitCoin and Cryptoasset Regulation: Recent Cases from Canada
By Richard Stobbe
In a recent pair of decisions, the law around bitcoin, crypto-assets and blockchain-enabled tokens is continuing to evolve:
1. 3iQ and “The Bitcoin Fundâ€
In 3iQ Corp (Re), 2019 ONSEC 37 (CanLII), the Ontario Securities Commission has ruled in favour of a bitcoin fund manager in an interesting decision that pits the development of a novel asset class (a bitcoin fund)Â against legal prospectus requirements, the public interest jurisdiction of the Securities Commission, and the purposes and principles of the Securities Act itself.
A fund manager – 3iQ – wanted to launch a so-called “bitcoin fund” to enable members of the public to invest in a managed fund that was dedicated to bitcoin. Initially, the Director denied a receipt for The Bitcoin Fund’s prospectus because of concerns about bitcoin, namely: concerns about the crypto-asset’s liquidity, integrity of the markets for that cryptocoin, and concerns about this fund’s ability to value and safeguard the asset and file audited financial statements.
In a hearing to appeal the initial refusal, the Commissioner issued reasons allowing the prospectus for this fund. Among the issues was the question of whether bitcoin is an “illiquid asset” as defined in NI 81‑102. If so, the proposed fund would not comply with the restriction against holding illiquid assets in section 2.4 of NI 81‑102. While the Commissioner did not go so far as to declare that bitcoin is NOT an illiquid asset, the conclusion was: “Staff has not demonstrated that bitcoin is an illiquid asset,” which arrives at the same point. As for the question of protecting the public interest, the Commissioner turned a bit philosophical about the role of the Securities Commission in acting as guardian of the public.
To take a risky asset like a bitcoin fund and “professionalize” the investment process by pooling investor funds under a professional management structure is a way to mitigate those risks – something that the Commission should encourage, not discourage.  “Capital market participants”, quipped the Commissioner, “should be encouraged to engage with the Commission, and not incentivized to avoid doing so.” This is the case especially when it provides an alternative to investors acquiring bitcoin through unregulated vehicles.
… And what do “unregulated vehicles” look like? That bring us to the next case.
2. The “Einstein Exchange” crypto-asset trading platformÂ
On November 1, 2019, the BC Securities Commission was concerned enough about rumours of imminent collapse at a cryptocoin exchange that it applied to court for an order appointing an interim receiver to seize and protect any assets of the so-called “Einstein Exchange”. The exchange was an unauthorized Vancouver-based crypto-asset trading platform. Better known as an “unregulated vehicle”.
Grant Thornton acted as interim receiver and as outlined in its Receiver’s Report, the receiver executed a Friday night search and seizure to sift through the allegations that the Einstein Group owed customers between $8 and $10 million USD. After itemizing the cash, assets, and the state of any cryptocurrency wallets under the control of the “Einstein Exchange”, the receiver determined that the Einstein Group had less than $45,000 in cash and cryptocurrency.
The receiver was quickly discharged and the BCSC investigation continues.
Calgary – 07:00 MT
No comments
The Scope of Crown Copyright
By Richard Stobbe
It’s time to update our 2015 post about copyright in survey plans!  In the course of their work, land surveyors in Ontario prepare a survey document, and that document is routinely scanned into the province’s land registry database. Copies of survey documents can be ordered from the registry for a fee.
Land surveyors commenced a copyright class action lawsuit against Teranet Inc., the manager of the land registry system in Ontario.  The case travelled all the way up to Canada’s top court and in Keatley Surveying Ltd. v. Teranet Inc.  2019 SCC 43 the Supreme Court of Canada (SCC) rendered a decision on the appeal: Copyright in plans of survey registered or deposited in the land registry office belongs to the Province of Ontario under s. 12 of the Copyright Act.
Section 12 of the Copyright Act provides a statutory basis for Crown copyright.
Under this section, the Crown holds copyright in any work “prepared or published by or under the direction or control of Her Majestyâ€.
The court aimed to balance the rights of the Crown in works that are prepared or published under the control of the Crown, where it’s necessary to guarantee the authenticity, accuracy and integrity of the works. However, the scope of Crown copyright should not expropriate the copyright of creators and authors.
Basically, Crown copyright applies where:
- The work is prepared by a Crown employee in the course of his or her employment or
- The Crown determines whether and how a work will be made, even if the work is produced by an independent contractor.
In both situations, the Crown exercises “direction and control†for the purposes of Section 12 of the Act.
In the Teranet case, the main question was whether the registered and deposited survey plans were published by or under the “direction or control†of the Crown. The court concluded that “When either the Crown or Teranet publishes the registered or deposited plans of survey, copyright vests in the Crown because the Crown exercises direction or control over the publication process.â€
Applying the principle of technological neutrality, the court indicated that the province’s use of new technologies (after digitization of the survey plans and publication process) did not change the court’s assessment of whether the Crown has copyright by virtue of s. 12. Finally, because the Crown owns copyright in the survey plans pursuant to s. 12 of the Act, there could be no infringement under the electronic registry system, and the class action was dismissed.
Background Reading:
Calgary – 07:00 MST
No commentsCanadian Smart Contract Law: Is it broke and do we need to fix it?
.
By Richard Stobbe
The idea of a ‘smart contract’ has been a lot of things: it’s upheld as the next big thing, a beacon of change for society, a nail in the coffin of an inefficient legal services profession, and it’s criticized as a misnomer for ‘dumb code’. Our review of smart contracts continues with this question: Are ‘smart contracts’ in need of specific laws and regulations in Canada?
In other words, is ‘smart contract’ law broken and in need of fixing?
(Need a quick primer on smart contracts? Can Smart Contracts Really be Smart?)
For those who may recall, the advent of other technologies has caused similar hand-wringing. For example the courts have, over the years, dealt with contract formation involving the telephone, radio, telex and fax … and email … yes, and the formation of contracts by tapping “I accept” on a screen.
There is a very good argument that the existing electronic transactions laws in Canada adequately cover the most common situations where so-called ‘smart contracts’ would be used in commercial relationships. For example, the Alberta Electronic Transactions Act (a piece of legislation that was introduced almost 20 years ago, when people talked about the “information superhighway”), was intentionally designed to be technology neutral.
The term “electronic signature†is defined in that law as “electronic information that a person creates or adopts in order to sign a record and that is in, attached to or associated with the record”. It’s so broad that the term can arguably apply to any number of possible applications, including situations where someone approves a transactional step within a smart contract work flow. Of course, this still has to be tested in court, where a judge would apply the law in an assessment of the specific facts of a particular dispute.
Does that create uncertainty? Yes, to a degree.
But the risks associated with that approach are preferable to the alternative. The alternative is to go the way of Arkansas, or other jurisdictions who have decided to wade in by prescriptively defining “smart contracts”.  For example, a 2019 law in Arkansas – “An Act Concerning Blockchain Technology†HB 1944 – amends that state’s electronic transactions law by defining “blockchain distributed ledger technology,†“blockchain technology†and “smart contract.â€Â By imposing specific definitions, these laws may have the unintended effect of excluding certain technologies that should be included, or catching use cases that were not intended to be caught. This would be the equivalent of trying, in 2001, to define an electronic transaction by looking at Amazon’s 1-click checkout. Sure, it was innovative at that time, but to peg a legal definition to that technology would have been short-sighted and unnecessarily constraining.
A second problem is a lack of standardization or uniformity in how different jurisdictions are choosing to define these technologies. This creates more uncertainty than a reliance on existing electronic transactions laws.
As blockchain and smart contract technology develops, the rush to have legal definitions cast in stone is premature and unwarranted.
Related Reading:
Calgary – 07:00 MST
No commentsClarity on IP Licenses and Bankruptcy
By Richard Stobbe
As we wrote about a year ago (See: What happens to IP on bankruptcy? ), we have been anticipating amendments to the Bankruptcy and Insolvency Act (BIA) and Companies’ Creditors Arrangement Act (CCAA) relating to IP licenses in cases where the IP licensor becomes insolvent. We now know that these changes will come into force November 1, 2019.
When it becomes law, Bill C-86 will enact changes to Canadian bankruptcy laws to clarify that intellectual property users can preserve their usage rights, even if:
- intellectual property rights are sold or disposed of in the course of a bankruptcy or insolvency proceeding, or
- if the trustee or receiver seeks to disclaim or cancel the license agreement relating to IP rights.
If the bankrupt company is an owner of IP, that owner has licensed the IP to a user or licensee, and the intellectual property is included in a sale or disposition by the trustee, the changes in Bill C-86 make it clear that the sale or disposition does not affect the licensee’s right to continue to use the IP during the term of the agreement. This is conditional on the licensee continuing to perform its obligations under the agreement in relation to the use of the intellectual property.
For more background, see:
Calgary 07:00 MST
No commentsRecent Blockchain-Related Enforcements and Exemptions
By Richard Stobbe
Securities regulators, including the US Securities and Exchange Commission (SEC) and the Ontario Securities Commission (OSC), have come down on Canadian blockchain-related (or distributed-ledger technology-based) businesses based on enforcement of traditional securities laws. Here are a few recent enforcement cases:
How do Securities Laws apply to Blockchain and Cryptocurrency?
It’s been a few years since securities regulators in Canada have weighed in on the evolving area of Blockchain-based coin offerings and cryptocurrencies, and how they intersect with securities laws.
Generally, we know that Canadian securities laws will apply if the business that is selling the securities is either conducting business from Canada, or if Canadian investors are involved.
A cryptocurrency sale might be akin to a sale of traditional or fiat currency, such as buying or selling US dollars or silver coins. That alone does not typically fall within the purview of the securities laws, since it’s not an “investment†in the sense of buying part of an enterprise where the expectation of profit comes from the efforts of others. Of course a buyer of US dollars or silver coins might hope to profit if the currency goes up in value, but simply acquiring currency, without more, is a transaction governed by financial services regulators, not securities regulators. Similarly, a buyer might acquire cryptocoins for the purpose of buying virtual products that are located within a video game platform, in which case, securities laws are likely not engaged.
However, where the coin sale is akin to an investment, similar to the traditional sale of shares of a company, then securities laws will apply.  That’s the position that regulators have taken. The value of the coin (or the stake in the company) may rise or fall depending on how successfully the business executes its plan using the capital raised, based on the sale of the cryptocoins.  This is the application of the so-called the Howey test, which has largely been adopted into Canadian law.
The short answer? Don’t assume that an offering of a cryptocurrency or cryptocoins will avoid the application of securities laws. There are many instances where securities compliance will be required. Make sure you get experienced advice on this. Here are a few recent enforcement examples:
NextBlock Global Limited (“NextBlockâ€)
In a recent settlement, the OSC imposed a fine against NextBlock and its founder Alex Tapscott for misleading statements to prospective investors in a private placement that raised approximately $20 million. Â The SEC also settled charges against NextBlock over the same set of facts.
In this case the infractions were not, as it turned out, related to the application of securities laws to an ICO (initial coin offering). Rather, the company was sanctioned for false statements within its offering memoranda.
NextBlock, a cryptocurrency venture capital firm paid over $1 million in fines and was pushed off its planned IPO as a result.
Kik Interactive Inc. (“Kikâ€)
In June, the SEC sued Kik [https://www.sec.gov/litigation/complaints/2019/comp-pr2019-87.pdf] , a Canadian social media company over a $100 million initial coin offering of “Kinâ€, a digital token or virtual coin, based on allegations that the ICO was not properly registered with the SEC. According to the complaint “More than 10,000 investors worldwide purchased Kin for approximately $100 million in U.S. dollars and digital assets – over half of this sum coming from investors located in the United States. However, Kik’s offer and sale of Kin was not registered with the SEC, and investors did not receive the disclosures required by the federal securities laws.â€
Kik’s position is reportedly that the coin offering is not an ICO and is more akin to a token offering would be used to buy goods and services, much like the example of a virtual coin that is used to acquire something inside a virtual gaming platform.
This is one to watch as regulators and market participants bring this before the courts to clarify where the lines are drawn.
ZED Network Inc. (“ZEDâ€)
On the other side of the, ahem, ledger, we have ZED, a Canadian company that is aiming to disintermediate global foreign exchange and remittance transfers. The company will be creating and selling tokens (the ZED token), for use on its software as a service platform (the ZED Network) to facilitate cross-border transfers.
Is this merely a token, falling outside securities laws, like a coin that would be used to trade on a gaming platform? Deciding not to take that chance, ZED sought an exemption within the OSC’s so-called ‘regulatory sandbox’, enabling ZED to distribute the tokens to investors, in order to raise capital and establish a user base in order to carry out its ZED Network plans.
By obtaining this exemption ZED has a sort of regulatory roadmap for compliance, provided it follows all of the criteria and conditions laid out in the exemption order.  The regulatory constraints will ensure that ZED avoids the fate of Kik, but they also impose certain compliance costs and set the rails for the business model (a bit more cumbersome to amend if changes are needed to respond to the marketplace).
This is another one to watch, to see how ZED is able to progress its business within the compliance apparatus established by the OSC.
Calgary – 07:00 MST
No commentsAnne with a © : Copyright infringement and the setting of a Netflix series
By Richard Stobbe
Is there copyright in the setting of a Netflix series?
It’s time for a dose of stereotypical Canadian culture, and you can’t do much better than another copyright battle over Anne of Green Gables! With Sullivan v. Northwood Media Inc., 2019 ONSC 9 (CanLII) we can add to the  long list of cases surrounding the fictional character Anne. This newest case deals with a copyright claim by Sullivan Entertainment against the producers of a CBC / Netflix version entitled “ANNE with an E†(2017).
First, a newsflash: The Anne of Green Gables books were written by Lucy Maud Montgomery and originally published beginning in 1908.
Sullivan, of course, is known as the producer of a popular television version of the Anne of Green Gables novels, starting with “Anne of Green Gables†(1985), the copyright in which is registered under Canadian Copyright Registration No. 358612.
Enter the latest incarnation of the AGG story, a CBC series produced by Northwood Media, now streaming on Netflix.
Sullivan alleges that Northwood, the producer of the latest Netflix version, has copied certain elements that were created by Sullivan in its TV series from the 1980s, elements that were not in the original novels. This copyright claim forces an examination of the scope or range of copying that is permitted around setting, plot concepts, imagery, and production or design elements.
Wait… are plot concepts and settings even protectable? In copyright law, we know that ideas are not, on their own, protectable; copyright protects the expression of ideas. Here, Sullivan as the owner of the copyright in its television production alleges that the Netflix series infringes copyright by copying scenes, not literally but through non-literal copying of a substantial part of the original protected work.
For example, Sullivan alleges that the Netflix version copies settings or conceptual elements such as:
- the decision to set the story in the late 1890s (the choice made in the Sullivan version), as opposed to the 1870s (the choice made by the original author in the Anne of Green Gables novel).
- the use of steam trains, replicated from a scene in one of the Sullivan episodes (apparently steam trains would not have been historically accurate in a 1870s setting);
- copying the concept and scene of a class spelling bee, to establish the rivalry between Anne Shirley and Gilbert Blythe;
- depictions and staging of scenes such as Anne’s life with the Hammond family or Matthew Cuthbert passing by the hose of Mrs. Lynde’s on his way to the train station to pick up Anne.
The allegations are not that the scenes are literally cut-and-paste from the original, but that the copying of settings, concepts and staging is copying of “a substantial part” of the original for the purposes of establishing copyright infringement.
In the words of the court in Cinar Corporation v. Robinson, 2013 SCC 73, copyright can protect “a feature or combination of features of the work, abstracted from it rather than forming a discrete part…. [T]he original elements in the plot of a play or novel may be a substantial part, so that copyright may be infringed by a work which does not reproduce a single sentence of the original.â€
(See our earlier article: Â Supreme Court on Copyright Infringement & Protection of Ideas )
The preliminary decision in Sullivan v. Northwood Media Inc. is about a pre-trial procedure related to document discovery, and once it goes to trial, the outcome will be interesting to see. This case is a series worth watching.
Calgary – 07:00 MT
No commentsCopyright, Obituaries, and $10 million in Statutory Damages
By Richard Stobbe
An obituary aggregation site – yes, there is such a thing – was in the business of reposting obituaries, both text and photos, taken from the sites of Canadian funeral homes and newspapers. This database of obituaries was a way to attract visitors who could then buy flowers and ‘virtual candles’ on the same page as the obituary, to generate profits.
Not surprisingly, someone complained.
Thomson v. Afterlife Network Inc., 2019 FC 545 (CanLII)Â was a class action lawsuit against the obituary aggregation company, Afterlife, for copyright infringement, based on the unauthorized copying and publication of over a million obituaries. Shortly after the class action lawsuit was launched, the Afterlife site shut itself down.
Class action members expressed that “an obituary they had written for a family member, often accompanied by a photograph, had been posted on Afterlife’s website without their permission. The evidence of many Class Members is that they had written the obituaries in a personal way and that their discovery that the obituaries had been reproduced with the addition of sales of candles and other advertising was an emotional blow to them. In some cases, inconsistent information was added, for example, inaccurate details about the deceased or options to order flowers where the family had specifically discouraged flowers. The Class Members also describe Afterlife’s conduct, in seeking to profit from their bereavement and in conveying to the public that the families were benefiting from sales of virtual candles or other advertising, as reprehensible, outrageous and exploitative.â€
The court had no trouble in establishing copyright protection for the obituaries as well as the photos.
The court also quickly concluded that Afterlife has republished this content without the permission of the original authors.
Damages need not be proven where statutory damages are invoked. Since statutory damages (Section 38.1 of the Copyright Act) allow for not less than $500 and not more than $20,000 per infringement, the court saw that the minimum of $500 multiplied by the estimated two million separate infringements (at least one photo plus a block of text in each of the 1 million copied obituaries), would result in a minimum damage award of around $1 billion.  Seeing this as grossly disproportionate, the court awarded $10 million in statutory damages, and another $10 million in aggravated damages, which can be awarded for compensatory purposes. Strangely, the court did not award punitive damages for this case of “obituary piracyâ€, that the court agreed was high-handed, reprehensible and “represents a marked departure from standards of decencyâ€.
Although this case may be noted for its significant statutory damage award, it also deal with a moral rights claim by the original authors of the obituaries. Under Canadian copyright law, “moral rights†protect the integrity of a work and are engaged where the author’s honour or reputation is prejudiced by the distortion or modification of the original work, or by using the work in association with a product, service, cause or institution.
The court struggled to find a moral rights infringement, since it was given evidence of the subjective elements of the infringement (the authors expressed that they were understandably mortified that others would think that they were somehow profiting from bereavement). However, the court noted that there is both a subjective and objective aspect in order to establish infringement of moral rights. The objective element was missing here.
In the end, a $20 million damage award was granted against Afterlife.
Calgary – 07:00 MT
No commentsCraft Beer Trademarks: The Ol’ Cease & Desist
By Richard Stobbe
Local Alberta breweries Elite Brewing (visited, love the carbon fibre bar) and Bow River Brewing have been on the receiving end of a cease and desist letter from the City of Calgary over a beer label for Fort Calgary ISA (a “richly hopped lighter bodied India session ale”).
The complaint by the City related to the unauthorized use of “FORT CALGARY”, which is an official mark owned by the City.
But wait, isn’t “FORT CALGARY” also an historical landmark and a place name?
From reading our other articles on geographical locations as trademarks, you might wonder how this works. You might say “Hang on… if a trademark is based on a geographic name, and a trademarks examiner decides that the geographic name is the same as the actual place of origin of the products, won’t the trademark be considered ‘clearly descriptive’ and thus unregistrable as a trademark? Furthermore, if the geographic name is NOT the same as the actual place of origin of the goods and services, the trademark will be considered ‘deceptively misdescriptive’ since the ordinary consumer would be misled into the belief that the products originated from the location of that geographic name. If that’s true, then how can a trademark owner assert rights over a geographic location?”
Yes, yes, that’s all true, with some exceptions, but according to Canadian trademark law there is also something called an official mark, which is what the City of Calgary owns. This is a rare species of super-mark that effectively sidesteps all of those petty concerns regarding geographical locations, ‘clearly descriptive’ and ‘deceptively misdescriptive’.
By virtue of its status as a government entity, the City can assert rights in certain marks that it adopts under Section 9 of the Trademarks Act.  These rights form the legal basis for the City’s recent cease and desist letter regarding the FORT CALGARY beer label.
This case has some unique elements due to the special rights that the City claims under the Trademarks Act, but the general message is the same: craft brewers can benefit from some preliminary trademark clearance searching when they launch a brand or a new beer name. And they should seek advice if they’re on the receiving end of this kind of letter.
In the end, the brewers reportedly agreed to sell out their remaining stock and refrain from further use of the Fort Calgary label, and the City agreed not to commence a lawsuit.
Need advice on beer trademarks and clearance searching? Contact craftlawyers.ca.
Calgary – 10:00 MT
No commentsAre we getting Canadian Regulations for Crypto Trading?
.
By Richard Stobbe
In February 2019, we reviewed the story of QuadrigaCX, and raised the question of how this would impact the adoption of cryptocurrencies or other tokens that are powered by the same blockchain or distributed ledger technologies (DLT) that underpin BitCoin. In particular we suggested that some regulatory oversight might be warranted. See: QuadrigaCX and the Missing Millions: A Crypto Cautionary Tale .
In March 2019 the Joint Canadian Securities Administrators (CSA) and IIROC (Investment Industry Regulatory Organization of Canada) issued a Proposed Framework for Crypto-Asset Trading Platforms (PDF). From a regulator’s perspective, many of these crypto-questions fall into the crack between CSA and IIROC.
Setting the stage to close that gap with regulatory engagement in Canada, the report notes that there are over 2,000 “crypto assets” in the wild, some trading for fiat currencies and others for various types of crypto-tokens, using over 200 different platforms. “Many of these Platforms,” say the report’s authors, “operate globally and without any regulatory oversight.”
There are a variety of crypto assets but currently they can generally be categorized from a regulatory perspective in one of two ways:
- Either they are akin to a commodity or currency, often referred to as “utility tokens”, which are created to allow holders to access or purchase goods or services on a DLT network. Crypto assets that are a “form of payment or means of exchange on a decentralized network, such as bitcoin”, says the report, “are not currently in and of themselves, securities or derivatives. Instead, they have certain features that are analogous to existing commodities such as currencies and precious metals”;
- Alternatively, crypto assets can be more akin to tokenized versions of traditional securities, derivatives or investment contracts, in the sense that they operate like shares in a company, or an interest in assets. If the crypto assets mimic the features of securities or derivatives, and are traded on an exchange platform, then that platform should be subject to existing securities regulatory requirements.
One of the regulatory problems is that the feature-sets of many crypto assets continually blur the lines between “currency” and “security”. Existing securities legislation may still apply to exchange platforms that offer trading of crypto assets even if those are tokens more like commodities, particularly where the investor’s contractual right to the cryptocurrency asset behaves like a security or derivative. Among the challenges that are unique to crypto exchange platforms is that these tokens and coins trade on a global basis, both on exchange platforms and off, both inside and outside regular trading hours, without any central source for pricing or reliable reference data. The values are “illiquid and highly volatile”. From a market surveillance point of view, this makes the regulatory enforcement uniquely challenging.
Essentially, the CSA/IIROC proposed platform framework would apply to “Crypto-Asset Trading Platforms” that are subject to securities legislation and that may not otherwise fit into other existing regulatory categories. Among the recommendations in the paper, crypto-trading platforms may have to become registered as investment dealers and meet compliance requirements for IIROC dealer and marketplace members.
Notably, this regulatory scheme would apply both to Platforms that operate in Canada and to those that have Canadian participants.
Enforcement is not really addressed here, but that’s another debate altogether.
The comment period is open until May 15, 2019.
Additional Reading: CSA Staff Notice 46-307 Cryptocurrency Offerings and CSA Staff Notice 46-308 Securities Law Implications for Offerings of Tokens, NI 21-101 Marketplace Operation, NI 23-101 Trading Rules and NI 23-103 Electronic Trading and Direct Access to Marketplaces.
Calgary – 07:00 MST
No commentsAttacking Bad Faith Trademark Registrations in Canada
By Richard Stobbe
There are a number of monumental changes coming soon (June, 2019) to the trademark regime in Canada. One small change was actually first introduced in 2018, a change that may come in handy in some trademark disputes once the rest of the new provisions are in force.Â
The concept of “bad faith†became a formal part of the Trademarks Act in Canada in late 2018, and it remains to be seen how it might be developed as a tool to prevent unmeritorious applications or registrations.Â
One of the fears among some trademark owners is the perception that “use†has been dropped as a requirement for registration, clearing a pathway for trademark squatters who file extortionist or opportunistic applications where legitimate use was never intended. In fact, “use†remains a fundamental requirement under Canadian trademark law, but it is true that under the revised Act, a “Declaration of Use†will be dropped as a necessary step before registration; it is currently required for applications filed on the basis of proposed use, and that requirement falls away under the revised  Act.
The ability to attack a trademark on the basis of “bad faith†is supposed to provide an easier way to challenge opportunistic applications which might be filed without any intention of actual commercial use. This is a new ground for invalidating a trademark registration or opposing an application, which is embedded in Section 18 of the Act (“The registration of a trade-mark is invalid …. if the application for registration was filed in bad faithâ€). There is no definition of “bad faith†in the Act but at least one Canadian case considered the issue several years ago:  HomeAway.com, Inc. v. Hrdlicka, 2012 FC 1467 (CanLII) Â
In HomeAway, the Federal Court considered a case where an individual, Mr. Hrdlicka, filed an application for the mark VRBO, and obtained a registration for that mark in association with “Vacation real estate listing servicesâ€.Â
The VRBO mark is, of course, an acronym for “vacation rental by ownerâ€, and a well-known brand owned by HomeAway.com Inc. Mr. Hrdlicka obtained registration of the mark in Canada because he apparently filed a blank “Declaration of Useâ€, thus somehow securing the registration despite the lack of any declaration of use, or any actual evidence of use in Canada. The Federal Court found that the applicant never used VRBO as a trade-mark in Canada (until dubious evidence emerged after the dispute arose), and that, at the time he applied to register that trade-mark in Canada, Mr. Hrdlicka was aware of HomeAway’s business. The evidence showed that he registered the mark for the purpose of selling it back to HomeAway “for a large sum of money and/or for employment or royalties.† This is reminiscent of many dot-ca domain name disputes.Â
As a result, the Federal Court concluded that Mr. Hrdlicka, in filing the application for registration, “had no bona fide intent of using it in a legitimate commercial way in Canada. His intent was to extort money or other consideration from HomeAway. Such activity should not be condoned or encouraged.†The court decided to expunge the registration, relying on its general powers under Section 57 of the Act.Â
This is precisely the circumstance that concerns current brand owners in light of the pending changes to the Trademarks Act: opportunistic registration, no bona fide purpose, and no evidence of actual use.
While the term “bad faith†does not actually appear in the HomeAway judgement, the result is clear: the application or registration of a mark without any bona fide intent or legitimate commercial use, will be considered to be filed for an improper purpose, and such conduct lacking good faith intent should be considered “bad faith†within the scope of Section 18(e). Â
It remains to be seen whether courts apply this decision to future Section 18(e) challenges.
Calgary – 07:00 MST
No commentsPrivacy Update: Will Consent be Required for Outsourcing Canadian Data?
By Richard Stobbe
Here’s a familiar picture: You are a Canadian business and you use a service provider outside of the country to process data. Let’s say this data includes personal information. This could be as simple as using Gmail for corporate email, or using Amazon Web Services (AWS) for data hosting, or hiring a UK company for CRM data processing services.Â
Until now, the Federal Office of the Privacy Commissioner (OPC) has taken the position that data processing of this type is a “use†of personal information by the entity that collected the data for the purposes of the Personal Information Protection and Electronic Documents Act (PIPEDA). Such use would require the consent of the individual for the initial collection, but would not require additional consent for the data processing by an out-of-country service provider, provided there was consent for that use at the time the information was first collected. Â
The privacy laws of some provinces contain notification requirements in certain cases, though not express consent requirements, for the use of service providers outside of Canada. For example, Alberta’s Personal Information Protection Act, Section 13.1, indicates that an organization that transfers personal information to a service provider outside Canada must notify the individual in question.Â
The OPC’s guidance, dating from 2009, took a similar approach, allowing Canadian companies to address the cross-border data processing through notification to the individual. In many cases, a company’s privacy policy might simply indicate in a general way that personal information may be processed in countries outside of Canada by foreign service providers. In the words of the commissioner in 2009: “[a]ssuming the information is being used for the purpose it was originally collected, additional consent for the transfer is not required.â€Â As long as consumers were informed of transborder transfers of personal information, and the risk that local authorities will have access to information, the organization was meeting its obligations under PIPEDA.Â
A recent consultation paper published by the OPC has signalled a potential change to that approach. If the changes are adopted by the OPC, this will represent a significant shift in data-handling practices for many Canadian companies.Â
Draft guidance from the OPC, issued April 9, 2019, indicates that recent high profile cross-border data breaches, such as the incident involving Equifax, have inspired a stricter consent-based approach. Today, the OPC issued a supplementary discussion document to explain the reasons for the proposed changes. (See: Consultation on Transborder Dataflows)
Reversing 10 years of guidance on this issue, the OPC now explains that a transfer of personal information between one organization and another should be understood as a “disclosure†according to the common understanding of that term in privacy laws.Â
If the draft guidelines are adopted by the OPC, any cross-border transfers of personal data to an outsourced service provider would be considered a “disclosureâ€, mandating a new consent, as opposed to a “use†which could be covered by the initial consent at the time of collection. Depending on the circumstances, the type of disclosure and the type of information, this could require express consent, and it’s not clear how this would apply to existing transborder data-processing agreements, or whether additional detail would be required for consent purposes, or if the specific names of the service providers would be required as part of the consent. This could significantly impact data-processing, e-commerce operations, and the consent practices of many Canadian businesses.Â
Consultations are open until June 4, 2019. Please stay tuned for further updates on this issue and if you want to seek advice on your company’s privacy obligations, please contact us.
Calgary – 16:00 MST
No commentsMeeting Mike Tyson does not constitute consideration for Canadian copyright assignment
By Richard Stobbe
When is a contract really a contract and when is it just a type of unenforceable promise that can be revoked or cancelled?
Glasz c. Choko, 2018 QCCS 5020 (CanLII) is a case about ownership of raw documentary footage of Mike Tyson, the well-known boxer, and whether an email exchange was enough to form a binding contract between a promoter and a filmmaker.
The idea of “consideration” is supposed to be one of the important elements of an enforceable contract. There must be something of value exchanging hands between two parties as part of a contract. But that “something of value” can take many forms. The old English cases talk about a mere peppercorn as sufficient consideration.
In this case, a boxing the promoter, Mr. Choko, promised a pair of filmmakers that he had a special relationship with Mike Tyson, and could give them special access to obtain behind-the-scenes footage of Mr. Tyson during his visit to Toronto in 2014. An email was exchanged on September 4, 2014, in which the filmmakers agreed that, in exchange for gaining this access, the copyright in the footage would be owned by the promoter, Mr. Choko.
The filmmakers later revoked their assignment.
The parties sued each other for ownership of the footage. Let’s unpack this dispute: the footage is an original cinematographic work within the meaning of section 2 of the Copyright Act. The issues are: Was the work produced in the course of employment? If not, was the copyright ownership to the footage assigned to Mr. Choko by virtue of the Sept. 4th email? And were the filmmakers entitled to cancel or revoke that assignment?
There was no employment relationship, that much was clear. And the filmmaker argued that the agreement was not an enforceable contract since there was a failure of consideration, and that the promoter misrepresented the facts when he insisted on owning the footage personally. In fact, he misrepresented how well he really knew the Tyson family, and mislead the filmmakers when he said that Mrs. Tyson has specifically requested that the promoter should be the owner of the footage. She made no such request.
The promoter, Mr. Choko, argued that these filmmakers would never had the chance to meet Mike Tyson without his introduction: thus, the experience of meeting Mr. Tyson should be enough to meet the requirement for “consideration†in exchange for the assignment of copyright. However, the court was not convinced: “every creative work can arguably be said to involve an experience…” If we accepted an “experience” as sufficient consideration then there would never be a need to remunerate the author for the assignment of copyright in his or her work, since there would always be an experience of some kind.
Take note: Meeting Mr. Tyson was insufficient consideration for the purposes of an assignment Canadian copyright law.
For advice on copyright issues, whether or not involving Mr. Tyson, please contact Richard Stobbe.
Calgary – 07:00 MDT
No comments